Cloud Communications Solutions: Why Every Cloud Voice Deployment Needs a Carrier-Grade SBC

Your cloud voice platform is only as secure as its edge. Every UCaaS deployment, CPaaS integration, and hosted SIP trunk terminates somewhere, and that termination point is where things get complicated. Unencrypted signaling, uncontrolled SIP traffic, and protocol mismatches between vendors are the default when nothing is actively managing that boundary.
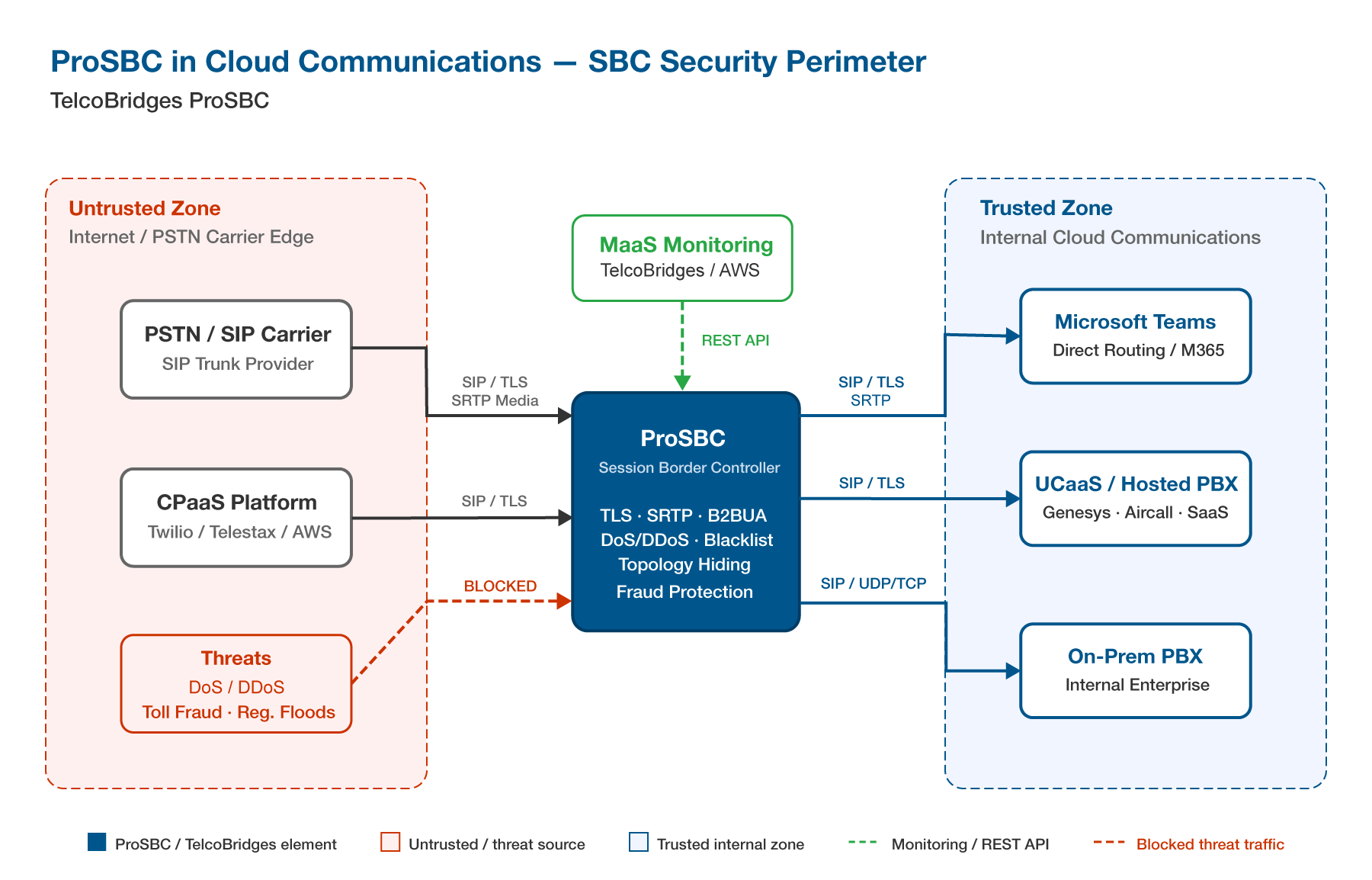
That’s where Session Border Controllers (SBCs) come in. An SBC sits at the edge of your voice network and acts as the enforcement point for security policy, media encryption, and protocol normalization. It’s what makes it possible to connect platforms that weren’t designed to talk to each other (carrier trunks to UCaaS systems, CPaaS APIs to PSTN infrastructure) without exposing internal topology or passing unencrypted traffic across that boundary.
Without one, the gap between your cloud voice platform and the carrier edge is unmanaged. With one, that gap becomes a controlled, auditable, encrypted handoff point.
What Makes a Cloud Communications Solution “Enterprise-Grade”?
Cloud communications spans a lot of territory: Microsoft Teams and Zoom Phone on the UCaaS side, Twilio and Telestax on the CPaaS side, hosted SIP trunking, CCaaS. Each platform has different signaling requirements and different carrier-edge trust models.
What they all have in common: they originate and terminate SIP traffic. And SIP wasn’t designed with security as a primary constraint. Connect any of these platforms directly to the public internet or a carrier trunk without an SBC, and you’re exposed to:
- SIP endpoints vulnerable to registration floods and DoS/DDoS traffic
- Signaling in plaintext unless TLS is explicitly enforced
- Unencrypted media unless SRTP is negotiated end-to-end
- Call failures and codec negotiation errors when vendor SIP dialects don’t align
A well-implemented SBC addresses all four. The key is architecture: SBCs that operate as a Back-to-Back User Agent (B2BUA) fully terminate each SIP leg and re-originate it, rather than simply proxying traffic. That distinction matters because it’s what enables topology hiding, header normalization, and independent security policy enforcement on each side of the connection. Not all SBCs implement this the same way, so it’s worth understanding what’s under the hood before deploying.
Where SBCs Fit in Cloud Communications
Microsoft Teams Direct Routing
Teams Direct Routing is how organizations connect an existing PSTN carrier to Microsoft 365 without going through Microsoft’s own calling plans. The architecture requires an SBC as the interconnect point between the carrier trunk and the Teams environment. Microsoft mandates SIP/TLS on port 5061 and SRTP for media, both of which are non-negotiable for certification. The SBC handles signaling translation, media encryption, and keeps the carrier relationship intact while telephony moves into the Microsoft 365 ecosystem.
CPaaS and SaaS SIP Trunking
CPaaS platforms like Twilio, Telestax, and Cloudoni expose programmable voice APIs, but they still terminate SIP trunks at the carrier edge. An SBC sits between the carrier and the CPaaS platform to manage trunk signaling, enforce traffic policies, and handle failover.
SaaS voice platforms introduce a different challenge: interoperability. Platforms like Aircall and Genesys each implement SIP in slightly different ways, and carrier trunks don’t always align with those dialects. SIP header manipulation at the SBC layer is what resolves those mismatches without requiring changes on either side.
Remote Worker Access Security
When employees access hosted voice applications over the public internet, SIP traffic travels across untrusted networks without additional controls. Applying SIP/TLS and SRTP at the SBC edge encrypts both signaling and media for those connections, removing the dependency on a VPN to secure voice traffic for distributed or remote teams.
Virtualized and Cloud Deployment
Software-based SBCs can run on standard hypervisors (VMware, KVM/Proxmox) as well as public cloud infrastructure (AWS, Azure) or bare metal servers. This removes the hardware procurement and refresh cycle from the equation and lets capacity scale with demand rather than being fixed at installation. Carrier-grade deployments in software are now routine, with modern SBC platforms handling tens of thousands of concurrent sessions per instance.
Security in Cloud Communications: What the SBC Edge Enforces
Security in cloud voice gets enforced at the SBC edge. Here’s what that looks like in practice.
Signaling and media encryption. SIP over Transport Layer Security (TLS) encrypts signaling traffic, typically on port 5061. SRTP encrypts media streams. A properly configured SBC also handles RTP-to-SRTP conversion at the edge, so media gets encrypted even when the originating endpoint sends plain RTP.
DoS and DDoS mitigation. SIP traffic is a common target for denial-of-service attacks. Protection rules at the SBC edge intercept malicious traffic before it reaches internal platforms.
Dynamic blacklisting and call access control. Allow/block rules at the network access point level can target specific IP ranges, calling numbers, or called numbers. Percentage-based greylisting adds another layer of control for traffic that falls into a grey zone.
SIP registration flood protection. Registration flood attacks are one of the most common threat vectors in hosted SIP trunk deployments. The SBC detects abnormal registration patterns and blocks them before they impact service.
Topology hiding. Internal IP addresses should never be visible to external parties. The SBC masks internal network topology, reducing the attack surface and preventing network mapping.
Real-time fraud protection. Per-call risk scoring against inbound and outbound traffic can be applied at the SBC layer, often via integration with dedicated fraud detection platforms such as TransNexus ClearIP, SecureLogix, or YouMail.
STIR/SHAKEN. For carriers and service providers subject to call authentication requirements, the SBC handles both call signing at origination and verification at termination. Certificate issuance itself is handled by an external authority; the SBC integrates with those services rather than issuing certificates directly.
Monitoring and High Availability for Cloud Voice
Production cloud voice requires both redundancy and visibility.
High Availability (1+1) configurations ensure that a standby instance takes over instantly if the primary fails, with no loss of active calls or service continuity. This is a baseline expectation for carrier-grade deployments, not an optional add-on.
On the monitoring side, some SBC vendors offer hosted monitoring services that remove the need to build and maintain internal monitoring infrastructure. Installation, configuration, and ongoing support are handled externally, which reduces operational overhead for teams that don’t want to run their own monitoring stack.
For teams that do want direct integration with existing systems, a well-equipped SBC should expose a RESTful API for remote status and configuration management, SNMP traps for network management system integration, CDR output in text and RADIUS format, Mean Opinion Score (MOS) scoring for call quality visibility, and live packet capture and call trace capabilities for troubleshooting.
This Is Where ProSBC Comes In
ProSBC is TelcoBridges’ software-based, carrier-grade SBC built to handle everything covered in this article:
- Secures SIP signaling with TLS and SRTP, hides internal topology, and blocks registration floods and DoS traffic
- Normalizes protocols between platforms that don’t natively interoperate
- Connects carrier trunks to Microsoft Teams via Direct Routing
- Integrates with CPaaS platforms including Twilio, Telestax, and Cloudoni
- Supports STIR/SHAKEN via TransNexus and Neustar
- Runs on VMware, KVM, AWS, Azure, and bare metal
- High Availability and hosted monitoring available
- Subscription-based licensing with a 30-day free trial
