Understanding SIP Signaling: Fundamentals of VoIP Call Control and Interoperability

Every voice call that travels through an IP network relies on a carefully orchestrated sequence of messages to establish the connection. SIP signaling is the protocol that controls this orchestration. Unlike the audio stream itself (which uses RTP), SIP is the control plane: it tells the network where to send the call, when to ring the destination, and when to hang up. Understanding SIP signaling is foundational for anyone working with VoIP networks, SIP trunking, or carrier interconnection.
How SIP Signaling Controls the Call
SIP (Session Initiation Protocol) is a request-response protocol similar in structure to HTTP, but designed specifically for establishing, modifying, and terminating real-time communications sessions. It operates by defining two primary roles: a User Agent Client (UAC) that initiates requests, and a User Agent Server (UAS) that receives and responds to them. These roles are implemented and controlled by Session Border Controllers and other network intermediaries.
The core SIP methods handle distinct phases of a call lifecycle. INVITE initiates a new session: when you dial a number, an INVITE message is generated. ACK confirms that the called party has answered and the connection is established. BYE terminates the session when either party hangs up. Additional methods like REGISTER manage user location services (allowing the network to know where to find a user), and OPTIONS queries a server’s capabilities.
SIP servers respond with status codes that mirror HTTP structure. Codes in the 1xx range (100 Trying, 180 Ringing) are informational. Codes in the 2xx range (200 OK) indicate success. 3xx codes signal redirection, 4xx codes indicate client-side errors (like “user not found”), 5xx codes reflect server problems, and 6xx codes represent global failures that should not be retried. These responses allow the calling side to understand what happened and whether it should retry.
SIP runs across three primary transport protocols: UDP (connectionless, typically port 5060), TCP (connection-based, also port 5060), and TLS (encrypted, port 5061). TLS is essential for secure carrier-to-carrier peering and compliance-driven environments. The choice of transport depends on network reliability requirements and security policies.
Understanding the Basic SIP Call Flow
The fundamental call flow reveals why SIP is so powerful for building interconnected networks. Here’s what happens when Alice calls Bob:
- Initiation: Alice’s phone generates an INVITE message and sends it toward Bob’s domain. This message includes critical information: Alice’s SIP URI (sip:alice@company.com), Bob’s target URI (sip:bob@provider.com), and a session description (the media codecs Alice’s phone supports).
- Routing: The INVITE traverses SIP proxies, SBCs, or other intermediaries that may rewrite certain headers to ensure the message reaches its destination. Each routing element adds a Via header so responses can find their way back.
- Ringing: When Bob’s phone receives the INVITE, it sends back a 180 Ringing response to alert Alice that the call is being processed and Bob’s phone is ringing.
- Answer: When Bob picks up, his phone sends a 200 OK response back to Alice along with Bob’s own session description (the codecs Bob’s phone supports). The two sides negotiate a common codec.
- Confirmation: Alice sends an ACK (acknowledgment) back to Bob to confirm receipt of the 200 OK. At this point, the signaling handshake is complete.
- Media Exchange: Independent of SIP, the two phones now establish an RTP (Real-time Transport Protocol) stream to carry the actual audio. SIP negotiated the connection; RTP carries the conversation.
- Termination: When either party hangs up, a BYE message is sent. The other party responds with 200 OK, and the session is closed.
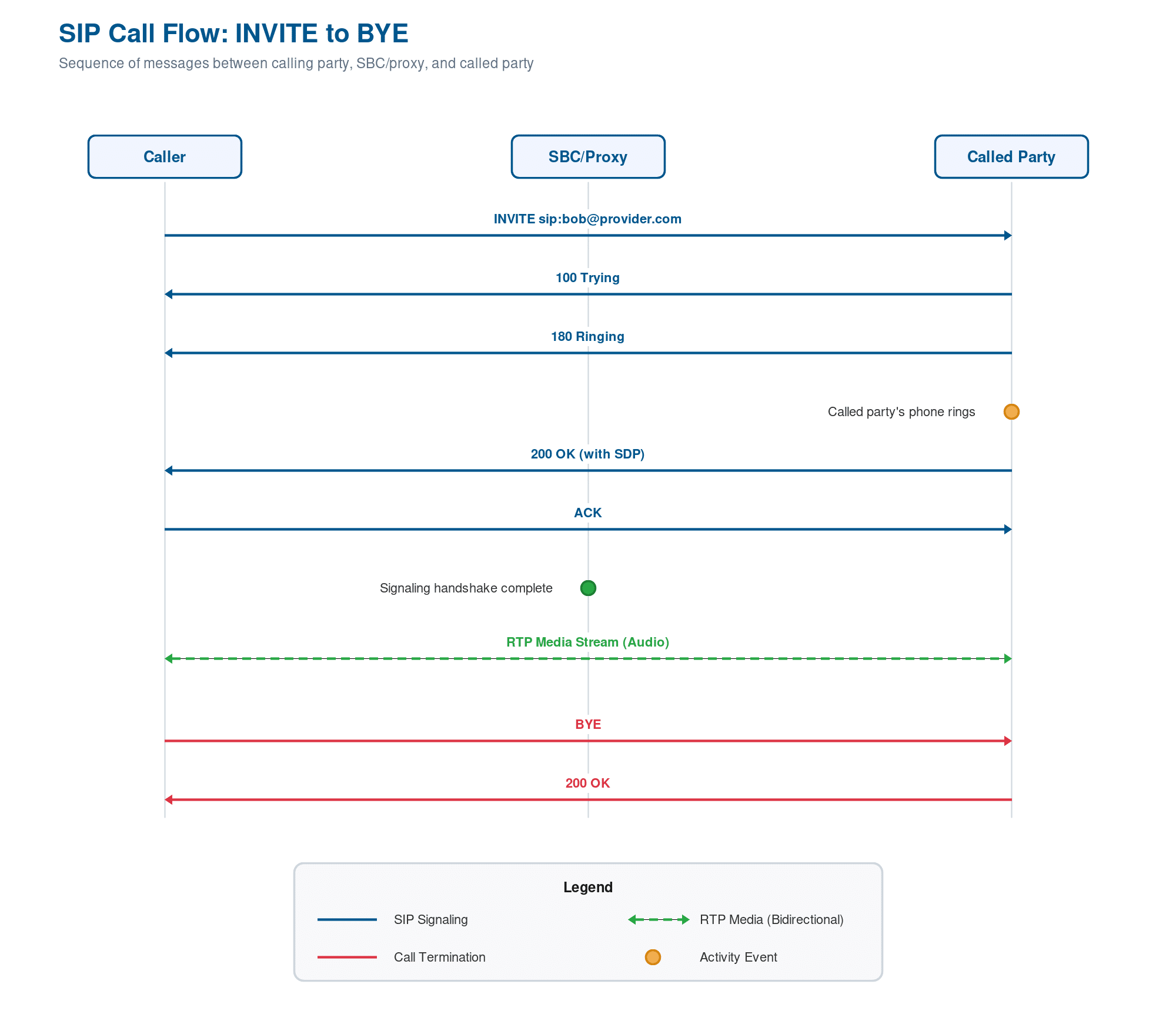
Click to enlarge.
This sequence is identical whether the call is between two phones in the same office or between carriers on opposite sides of the world. The beauty of SIP is that intermediaries (SBCs, proxies) can inspect and manipulate the signaling without touching the audio.
SIP Headers and Message Anatomy
Every SIP message contains three main parts: a request or status line, a set of headers, and an optional message body.
The request line for an INVITE looks like: INVITE sip:bob@provider.com SIP/2.0. The status line for a response looks like: SIP/2.0 200 OK.
Critical headers include:
From identifies the originating user. It carries the caller’s SIP URI and a tag that identifies this particular call leg. Example: From: <sip:alice@company.com>;tag=12345
To identifies the destination user. Example: To: <sip:bob@provider.com>;tag=67890 (the tag is added by the UAS when it responds).
Via records the path the INVITE traveled so responses find their way back. If the INVITE passed through two proxies, there will be two Via headers stacked in order. This prevents routing loops and ensures responses traverse the same path in reverse.
Contact tells the other party where to send future requests for this session. This is often the actual IP address and port of the endpoint.
CSeq is a sequence number (Command Sequence) that prevents out-of-order message processing. Each new request increments this number.
SIP header manipulation is a critical function of SBCs. Different vendors’ implementations sometimes expect slightly different header values or ordering. An SBC’s SIP header manipulation engine can rewrite headers in real time to bridge these incompatibilities, allowing carriers to peer with multiple vendors seamlessly.
SIP Proxies vs. B2BUA
Understanding the difference between these two architectural approaches is key to grasping how SBCs work in production networks.
A SIP Proxy is transparent. It forwards SIP messages between endpoints without generating its own calls. When an INVITE arrives, the proxy inspects the destination, queries routing tables, and forwards it onward. The proxy doesn’t originate a new INVITE; it just routes the existing one. This keeps the proxy lightweight and allows it to scale, but the proxy does not control the audio stream and has limited ability to enforce policy across the call.
A B2BUA (Back-to-Back User Agent) is opaque. It terminates the incoming SIP call completely (sending a 200 OK response to the caller) and then generates a new, independent INVITE to the destination. From the caller’s perspective, the B2BUA is the callee. From the destination’s perspective, the B2BUA is the caller. This architecture gives the B2BUA complete control over both call legs. It can enforce policies, manipulate SIP headers, transcode media, and manage routing on a per-call basis.
Session Border Controllers (SBCs) are B2BUAs. This is why they’re so effective at enabling multi-vendor interoperability. By terminating and re-originating calls, an SBC can inspect the SIP signaling, normalize it to match the downstream system’s expectations, and control how both sides see the call.
Why SIP Signaling Matters for Interoperability
SIP is a standards-based protocol, but vendors implement it with different interpretations. One vendor might include a particular header that another vendor’s system doesn’t expect. A third vendor might reorder headers in a way that breaks a competitor’s parser. One implementation might respond to INVITE within 100 milliseconds; another might take 500 milliseconds.
This is where SIP normalization becomes essential. An SBC can inspect every incoming SIP message and rewrite it to match the profile of the downstream system. It can remove unexpected headers, add missing ones, reorder them, or modify their values. Without this normalization, multi-vendor peering becomes brittle. A call from Vendor A’s system might fail when routed directly to Vendor B’s system, but succeed when an SBC acts as an intermediary.
The practical consequence: carriers managing diverse networks of PBXs, contact centers, cloud platforms, and upstream trunking providers rely on SBCs to bridge these incompatibilities. SIP signaling normalization is the backbone of large-scale, multi-vendor VoIP networks.
Conclusion
SIP signaling is the control-plane protocol that orchestrates every VoIP call, from initial setup through final termination. It’s a request-response architecture that allows intermediaries to inspect, route, and manipulate call flows without touching the media. Understanding the basic call flow (INVITE, 180 Ringing, 200 OK, ACK), the role of headers like Via and Contact, and the architectural difference between proxies and B2BUAs provides the foundation for designing, deploying, and troubleshooting VoIP networks.
For enterprises and carriers building multi-vendor networks, the ability to normalize SIP signaling across different platforms is critical to reliability. That’s where a B2BUA architecture (like the one at the heart of a Session Border Controller) becomes invaluable.
ProSBC and Intelligent SIP Signaling
SIP signaling is vendor-agnostic, but the implementation of an SBC determines how effectively it can bridge different vendor dialects. ProSBC operates as a true B2BUA, giving it complete control over SIP signaling on both the incoming and outgoing call legs. This means ProSBC can inspect every SIP message, validate it against your policy rules, normalize headers for downstream systems, and route calls based on complex criteria embedded in the signaling itself.
ProSBC includes a built-in SIP header manipulation engine that allows you to rewrite headers in real time, removing vendor-specific fields, adding required headers, or translating between different SIP dialects. This capability has proven essential for enterprises integrating multiple PBX platforms, contact centers moving to the cloud, and carriers managing interconnections with upstream providers.
For secure carrier-to-carrier peering, ProSBC supports SIP over TLS (encrypted signaling), ensuring that the control plane is protected from eavesdropping and tampering. Combined with SRTP for media encryption, this provides end-to-end security for voice communications.
Prefer to evaluate on your own first? Start your 30-day free trial.
