VoIP Security: The Service Provider’s Guide to Protecting Voice Networks

Voice networks carry billions of calls every day, and the infrastructure behind them is under constant attack. The Communications Fraud Control Association (CFCA) estimates that telecom fraud costs the industry more than $6.69 billion annually, with toll fraud and International Revenue Share Fraud (IRSF) among the largest contributors. SIP flooding and DDoS attacks can take down an entire voice platform in minutes. Caller ID spoofing erodes trust in the phone network itself, and the FCC has responded with STIR/SHAKEN mandates that every voice service provider must now satisfy.
If you operate a voice network (whether you are an ISP managing SIP trunk infrastructure, an MSP reselling voice services, a UCaaS or CCaaS vendor running a hosted platform, or a contact center protecting inbound call quality), VoIP security is not a feature you evaluate. It is the foundation your business runs on.
This guide is written for the people who build and operate voice networks, not for businesses choosing a phone system. It covers the real threats targeting carrier-grade infrastructure, the protocols and practices that defend against them, and how a Session Border Controller (SBC) enforces security at the network edge where it matters most.
Why VoIP Networks Are Vulnerable
VoIP was designed for interoperability, not security. The Session Initiation Protocol (SIP) that underpins virtually all modern voice signaling was standardized in an era when the primary concern was getting different vendors’ equipment to exchange calls, not defending against adversaries actively probing for weaknesses. That architectural decision has consequences that every voice network operator faces today.
SIP and RTP Were Built in the Clear
SIP signaling and RTP media travel as plaintext by default. Without explicit encryption, anyone with access to the network path can read SIP INVITE messages to see who is calling whom, capture RTP streams to reconstruct entire conversations, and extract authentication credentials from SIP REGISTER exchanges. The protocols themselves do not enforce confidentiality; that responsibility falls to the network operator.
Internet Exposure Multiplies Attack Surface
Unlike legacy TDM networks that ran over dedicated circuits, VoIP infrastructure is reachable over the public internet. SIP endpoints, registration servers, and trunk groups all listen on known ports (5060/UDP, 5060/TCP, 5061/TLS). Automated scanning tools can discover and fingerprint SIP infrastructure within minutes, and the barrier to launching a SIP flood or brute-force registration attack is essentially zero: open-source tools like SIPVicious are freely available.
Multi-Tenant Infrastructure Concentrates Risk
Service providers (ISPs reselling SIP trunks, MSPs managing voice for dozens of business customers, UCaaS platforms hosting thousands of tenants) run multi-tenant infrastructure where a single compromised endpoint can affect every customer on the platform. A toll fraud attack originating from one subscriber’s misconfigured PBX can generate tens of thousands of dollars in fraudulent charges before anyone notices. A DDoS attack targeting the provider’s SBC or registrar can take down voice service for every tenant simultaneously.
The Most Common VoIP Security Threats
Understanding the threat landscape is the first step toward defending against it. These are the attacks that voice network operators encounter most frequently, ranked by the financial and operational damage they cause.
SIP Flooding and DDoS Attacks
SIP flooding overwhelms voice infrastructure by sending massive volumes of SIP INVITE, REGISTER, or OPTIONS messages faster than the target can process them. The result is call setup failure for every legitimate user on the platform. Distributed denial-of-service (DDoS) attacks amplify this by coordinating floods from thousands of source addresses simultaneously, making simple IP-based blocking ineffective. Service providers have reported sustained attacks generating over 1,500 malicious calls per day from real phone numbers, a pattern known as Telephony Denial of Service (TDoS) that is particularly difficult to filter because each individual call appears legitimate.
Toll Fraud and International Revenue Share Fraud (IRSF)
Toll fraud remains the single most costly VoIP security threat. Attackers compromise a SIP trunk or PBX, then route calls to premium-rate international numbers they control, often in high-cost destinations where per-minute charges exceed $1. The attacker collects a share of the revenue while the service provider or subscriber receives the bill. IRSF is a $6.69 billion annual problem according to the CFCA, and it typically happens overnight or over weekends when traffic anomalies are least likely to be noticed.
Traffic pumping operates on a similar principle but targets domestic access-stimulation numbers. Subscription fraud involves obtaining SIP trunks or endpoints using stolen credentials specifically to generate fraudulent traffic.
Caller ID Spoofing and Robocalls
SIP spoofing exploits the fact that the From header and P-Asserted-Identity (PAI) in a SIP INVITE can be set to any value by the originating device. Without authentication, a bad actor can present any caller ID they choose, impersonating banks, government agencies, or the subscriber’s own customers. The FCC’s STIR/SHAKEN mandate exists specifically to address this, but compliance requires infrastructure changes at the SBC layer.
Robocall campaigns use spoofed caller ID at industrial scale. The FCC’s Robocall Mitigation Database requires every voice service provider to file a certification describing the steps they take to prevent illegal robocall traffic from originating on their network.
Registration Hijacking
Registration hijacking occurs when an attacker sends forged SIP REGISTER messages to redirect a legitimate user’s calls to a different endpoint. If the registrar accepts the forged registration, inbound calls intended for the real user are delivered to the attacker. Brute-force registration scanning (automated attempts to guess SIP credentials) is the most common vector, and unprotected registrars can receive thousands of registration attempts per hour.
Eavesdropping and Media Interception
Eavesdropping is the most direct consequence of unencrypted RTP. An attacker who can capture packets on the network path between two endpoints can reconstruct the audio of any call in real time. Even if signaling is encrypted with TLS, media traveling as plaintext RTP remains fully exposed. For service providers handling healthcare, financial, or legal communications, this is both a security risk and a compliance failure.
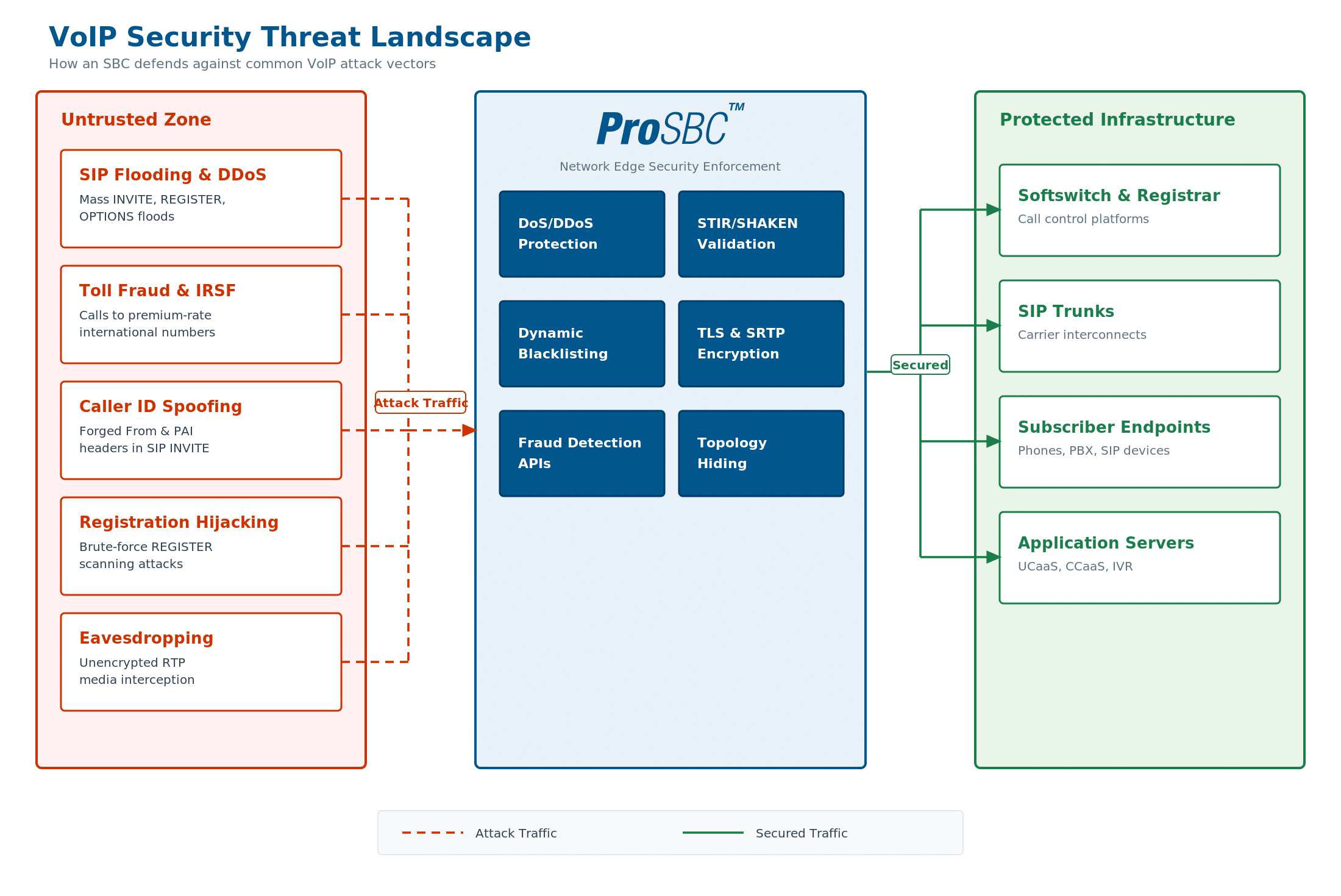
Common VoIP security threats targeting service provider infrastructure. The SBC sits at the network edge, inspecting and filtering both signaling and media before threats reach internal systems. Click to enlarge.
VoIP Security Best Practices for Service Providers
Securing a voice network is not a single technology decision; it is a layered defense strategy where each control reinforces the others. These best practices apply specifically to ISPs, MSPs, and platform operators managing carrier-grade SIP infrastructure.
Encrypt Everything: TLS for Signaling, SRTP for Media
Encryption is the baseline. SIP over TLS protects signaling from eavesdropping and credential theft. SRTP protects media from interception and recording. Both should be enforced on every external-facing trunk group, and ideally on internal legs as well. Platforms like Microsoft Teams Direct Routing and WebRTC will not connect to endpoints that lack TLS and SRTP, and compliance frameworks in healthcare and financial services increasingly require end-to-end voice encryption.
A B2BUA SBC is essential here because it terminates and re-originates both signaling and media on each call leg independently. This allows the SBC to accept unencrypted RTP from a legacy carrier on one side and deliver SRTP to a Teams or WebRTC endpoint on the other, without requiring either side to change its configuration.
Deploy SIP Rate Limiting and Anomaly Detection
Rate limiting caps the number of SIP transactions (INVITEs, REGISTERs, OPTIONSes) that any single source can send within a time window. This is the first line of defense against SIP flooding, brute-force registration scanning, and enumeration attacks. Anomaly detection goes further by identifying traffic patterns that deviate from established baselines: a sudden spike in calls to high-cost international destinations, an unusual number of short-duration calls, or registration attempts from geographic regions where the provider has no subscribers.
Implement Dynamic Blacklisting and Access Control
Static access control lists (ACLs) define which IP addresses and SIP domains are permitted to send traffic to your infrastructure. Dynamic blacklisting extends this by automatically blocking sources that trigger security rules. A source that sends 500 failed REGISTER attempts in a minute, for example, gets blacklisted without operator intervention. Percentage-based greylisting offers a middle ground: rather than fully blocking a suspicious source, the SBC can throttle its traffic to a configurable percentage while the operator investigates.
Hide Your Network Topology
Topology hiding replaces internal IP addresses in SIP headers with the SBC’s public address before any message leaves the network. Without it, Via headers, Contact headers, and Record-Route entries can expose internal server addresses, network structure, and even software versions to external parties. Attackers use this information to identify and target specific infrastructure components behind the SBC.
Enforce Call Routing Restrictions
Call routing restrictions prevent compromised endpoints from generating outbound calls to destinations the operator has not authorized. This includes blocking calls to known premium-rate number ranges, setting per-trunk concurrent call limits, restricting international dialing to explicitly allowed country codes, and enforcing time-of-day policies that flag off-hours traffic spikes for review. For MSPs managing multiple business customers, per-tenant call policies ensure that a compromise affecting one customer cannot generate charges or disruption for others.
Monitor Traffic in Real Time
No static defense catches every attack. Continuous monitoring of call detail records (CDRs), SIP message logs, and traffic dashboards allows operators to identify anomalies as they develop, before a toll fraud event has time to accumulate significant charges or a DDoS attack has time to degrade service quality for all subscribers. Automated alerting thresholds (calls per second, failed registrations, calls to flagged destinations) turn monitoring from passive observation into active defense.
SIP Trunk Security
SIP trunks are the arteries of a voice network, carrying signaling and media between carriers, platforms, and subscribers. For ISPs and MSPs operating SIP trunk infrastructure, trunk-level security is where VoIP security becomes operationally specific.
Secure the Peering Point
Every SIP trunk terminates at a peering point, the network boundary where your infrastructure connects to a carrier, a customer, or another provider. This is where an SBC operates as the voice network’s perimeter firewall. The SBC inspects every SIP message entering and leaving the trunk, enforces encryption policies, validates source addresses against access control lists, and applies SIP header manipulation rules that normalize traffic from different carriers into a consistent internal format.
Without an SBC at the peering point, your registrar, softswitch, and application servers are exposed directly to the public internet, along with every scanner, flood, and exploit attempt that comes with it.
Per-Trunk Security Policies
Not every trunk carries the same risk profile. A trunk peered with a Tier 1 carrier over a private interconnect presents different security considerations than an internet-facing trunk serving hundreds of SMB PBX endpoints. The SBC should allow per-trunk (per-NAP) security policies: different TLS requirements, different rate limits, different blacklisting thresholds, and different call routing restrictions for each trunk group. This granularity prevents a single security policy from being either too permissive for high-risk trunks or too restrictive for trusted peers.
Protect Against SIP Registration Scanning
SIP registration scanning is a constant background threat on internet-facing SIP infrastructure. Automated tools cycle through IP ranges, sending SIP REGISTER messages with common username/password combinations. The SBC should detect registration scanning patterns (high volumes of failed REGISTER responses from a single source) and block the source dynamically before a credential is guessed. SIP registration scanning protection is a distinct security function from generic rate limiting and should be configured explicitly.
Toll Fraud Prevention
VoIP fraud prevention is not a theoretical exercise. Toll fraud is an operational reality that costs the telecom industry billions every year. For service providers, a single undetected fraud event can generate five- or six-figure charges in a matter of hours.
How Toll Fraud Works
The typical IRSF attack follows a predictable pattern. The attacker compromises a SIP endpoint — often a misconfigured PBX, a device with default credentials, or a trunk with weak authentication. They then route calls through the compromised endpoint to premium-rate international numbers they control, often in high-cost African, Eastern European, or Pacific Island destinations where per-minute termination charges are highest. The attacker collects a revenue share from the premium number operator. Calls are typically placed overnight or over weekends to maximize the window before detection.
Traffic pumping follows a similar financial model but targets domestic access-stimulation numbers, exploiting inter-carrier compensation mechanisms to generate revenue from artificially inflated call volumes.
How SBCs Detect and Block Toll Fraud
An SBC positioned at the network edge can detect and block toll fraud through several complementary mechanisms. Call routing restrictions prevent calls to known high-risk destinations unless explicitly authorized. Concurrent call limits per trunk or per subscriber cap the volume of simultaneous calls any single endpoint can generate. Call duration limits flag and terminate calls that exceed a configurable threshold; legitimate business calls rarely last two hours, but fraud calls often do.
Real-time traffic analysis identifies anomalous patterns: a sudden spike in calls to a country code that normally receives zero traffic, a jump in short-duration calls (used to test routes before launching full-volume fraud), or off-hours call volume that deviates from the subscriber’s historical baseline.
Advanced fraud detection integrates the SBC with external fraud intelligence services. TransNexus ClearIP provides real-time fraud scoring and routing recommendations. JeraSoft delivers billing-aware fraud analytics. The SBC’s API and routing script engine can query these services during call setup, before the call is ever connected, and apply block, allow, or redirect decisions based on the fraud score returned.
STIR/SHAKEN Compliance
The FCC’s STIR/SHAKEN mandate is the most significant regulatory change to affect voice service providers in the past decade. Under the TRACED Act, every originating and terminating voice service provider must implement caller ID authentication using the STIR/SHAKEN framework, and the requirements continue to tighten.
What STIR/SHAKEN Does
When an originating service provider places a call, the STIR/SHAKEN framework requires the provider to cryptographically sign the call with a digital certificate, generating a PASSporT (Personal Assertion Token) that is inserted into the SIP INVITE’s Identity header. The token contains claims about the call’s origin (the calling number), destination, timestamp, and an attestation level (A, B, or C) reflecting the provider’s confidence in the caller’s identity.
The terminating service provider validates the signature against the originating provider’s certificate to confirm that the calling number was legitimately asserted. If the signature is invalid or missing, the terminating provider can flag, redirect, or block the call.
Attestation Levels
Full Attestation (Level A) means the originating provider has authenticated the calling party and confirmed they are authorized to use the calling number. Partial Attestation (Level B) means the provider originated the call and knows the source, but cannot verify the caller’s right to use the specific number. Gateway Attestation (Level C) means the call entered the provider’s network from an untrusted source, typically a TDM interconnect or international gateway, and the provider cannot verify the caller’s identity.
Implementation at the SBC Layer
STIR/SHAKEN signing and verification happen at the SBC because the SBC is the device that originates and terminates SIP sessions at the network boundary. The SBC sends signing requests to an external STIR/SHAKEN signing service, receives the signed Identity header, and inserts it into the outbound SIP INVITE. On the terminating side, the SBC extracts the Identity header from the inbound INVITE and sends a verification request to validate the signature.
An open integration model matters here. Some SBC vendors use proprietary STIR/SHAKEN implementations that lock the provider to a specific signing service partner. A flexible SBC integrates with any third-party signing service (TransNexus ClearIP, Neustar, or others) through standard HTTP-based APIs and configurable routing scripts, giving the provider full control over their STIR/SHAKEN partner choice.
Robocall Mitigation Database
The FCC requires every voice service provider to file a certification in the Robocall Mitigation Database describing the steps they take to prevent illegal robocall traffic from originating on their network. Providers that fail to file, or that file an insufficient plan, risk having their traffic blocked by downstream carriers. SBC-enforced call authentication, combined with fraud detection integrations, forms the technical foundation of a credible robocall mitigation filing.
How Session Border Controllers Enforce VoIP Security
Every threat discussed in this guide (SIP flooding, toll fraud, caller ID spoofing, registration hijacking, eavesdropping) converges at the network edge. The Session Border Controller is the enforcement point where security policies are applied to every call, every registration, and every SIP message entering or leaving the network.
Perimeter Defense: The SBC as Voice Firewall
An SBC operating as a B2BUA fully terminates every SIP session on one side and re-originates a new, independent session on the other. Nothing passes through unchanged. This architectural model gives the SBC the ability to inspect, modify, filter, or block any element of the signaling or media path — capabilities that a SIP proxy, which merely forwards messages, fundamentally cannot provide.
Mapping Threats to SBC Capabilities
| Threat | SBC Security Capability |
|---|---|
| SIP flooding / DDoS | Line-rate DoS/DDoS protection, SIP rate limiting, dynamic blacklisting |
| Toll fraud / IRSF | Call routing restrictions, concurrent call limits, fraud detection API integration (TransNexus, JeraSoft) |
| Caller ID spoofing | STIR/SHAKEN signing and verification, P-Asserted-Identity validation |
| Registration hijacking | SIP registration scanning protection, registration rate limiting, dynamic blacklisting |
| Eavesdropping | TLS for SIP signaling, SRTP for media, per-leg encryption management |
| Network reconnaissance | Topology hiding, SIP header manipulation |
Programmable Security Through APIs
Static security rules cover known threats. Programmable security covers everything else. An SBC with an API and routing script engine can query external systems during call setup (checking a fraud database, performing a CNAM lookup, validating a caller against a CRM) and make real-time routing decisions based on the response. This extensibility turns the SBC from a fixed security appliance into a programmable security platform that adapts to new threats without firmware updates.
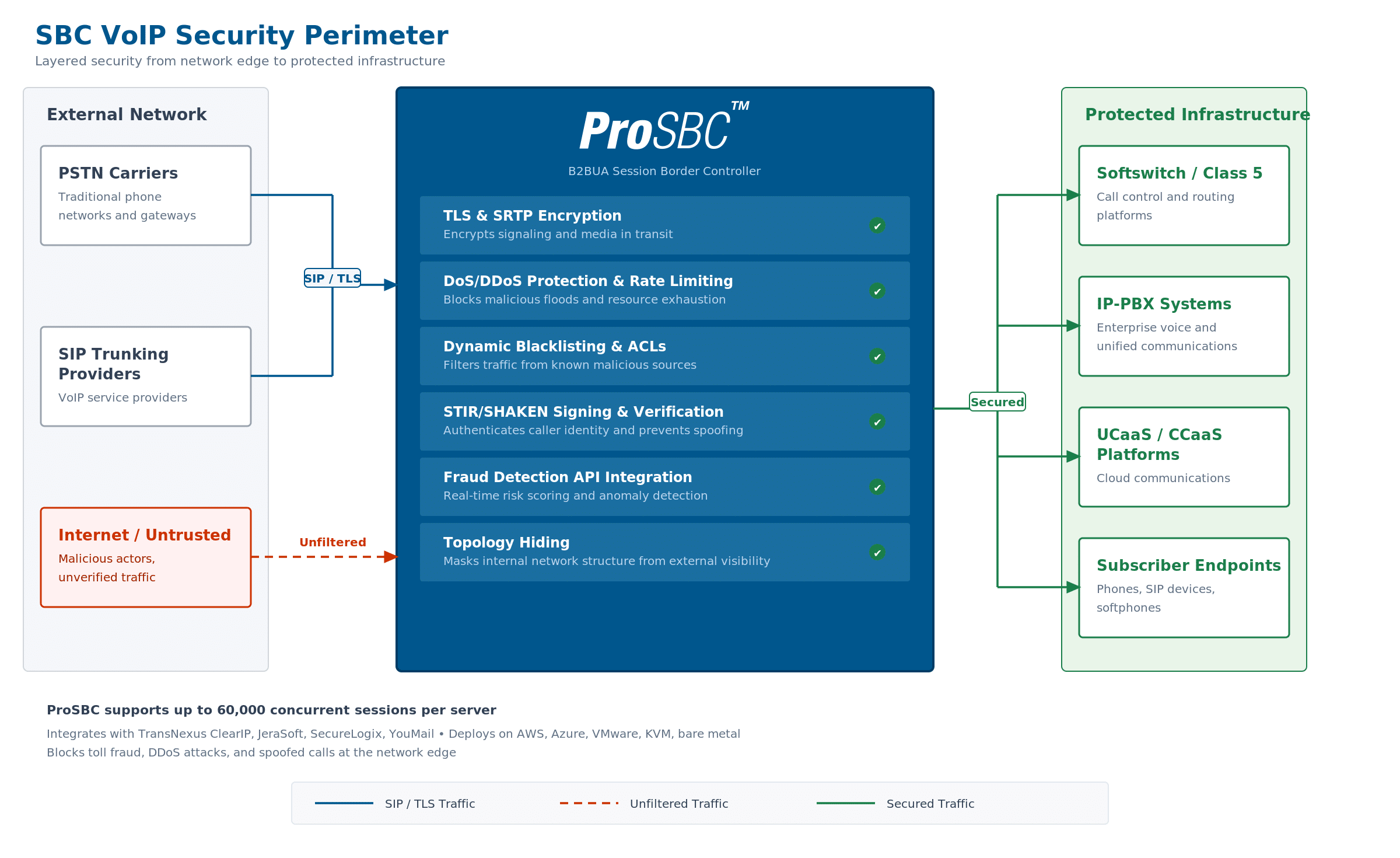
The SBC as voice network security perimeter. Every call traverses the SBC, where encryption, access control, fraud detection, and caller authentication are enforced before traffic reaches internal infrastructure. Click to enlarge.
Frequently Asked Questions
What is VoIP security and why does it matter for service providers?
VoIP security encompasses the protocols, technologies, and operational practices that protect voice-over-IP infrastructure from attacks, fraud, and unauthorized access. For service providers (ISPs, MSPs, UCaaS vendors, and contact centers), VoIP security is critical because a single breach can disrupt service for every customer on the platform, generate massive fraudulent charges, and create regulatory compliance exposure.
What are the biggest VoIP security threats?
The most damaging threats to service provider voice networks are toll fraud and IRSF (costing the industry over $6.69 billion annually), SIP flooding and DDoS attacks (which can take down an entire voice platform), caller ID spoofing (which undermines trust and triggers regulatory action), and registration hijacking (which redirects legitimate calls to attackers). Each of these threats targets the SIP signaling or RTP media layer and requires enforcement at the network edge.
How does an SBC protect against VoIP DDoS attacks?
An SBC protects against DDoS attacks through line-rate traffic inspection, SIP rate limiting that caps the number of transactions any source can send per second, dynamic blacklisting that automatically blocks sources exhibiting attack patterns, and SIP registration scanning protection that detects and blocks brute-force credential attacks. Because the SBC sits at the network edge as a B2BUA, it absorbs and filters malicious traffic before it reaches internal softswitch, registrar, or application infrastructure.
What is STIR/SHAKEN and does my SBC need to support it?
STIR/SHAKEN is the FCC-mandated framework for caller ID authentication. If you originate or terminate voice calls in the United States, your infrastructure must support STIR/SHAKEN signing (for originating calls) and verification (for terminating calls). The SBC is the device that performs signing and verification at the network boundary by integrating with an external STIR/SHAKEN signing service through standard HTTP-based APIs.
What is the difference between SIP security and VoIP security?
SIP security focuses specifically on protecting the SIP signaling protocol: encrypting SIP messages with TLS, validating SIP headers, preventing SIP flooding and registration attacks. VoIP security is broader, encompassing SIP security plus media encryption (SRTP), fraud prevention, caller authentication (STIR/SHAKEN), network topology protection, and operational monitoring. A comprehensive VoIP security strategy addresses both signaling and media, both protocol and business logic.
How can I prevent toll fraud on my voice network?
Toll fraud prevention requires multiple layers working together: call routing restrictions that block unauthorized international destinations, concurrent call limits per trunk and per subscriber, real-time traffic monitoring with automated anomaly alerting, and integration with fraud intelligence services (such as TransNexus ClearIP or JeraSoft) that score calls during setup and block high-risk traffic before it connects. All of these controls are enforced at the SBC.
Further Reading
FCC STIR/SHAKEN own-certificate rule — Learn how the FCC’s latest STIR/SHAKEN ruling affects your certificate infrastructure and what steps you need to take before the September 2025 deadline. See our detailed breakdown of the FCC STIR/SHAKEN own-certificate rule.
Protect Your Voice Network with ProSBC
ProSBC is a carrier-grade, software-based Session Border Controller built for the security challenges service providers face every day. It delivers line-rate DoS/DDoS protection, dynamic blacklisting with percentage-based greylisting, SIP registration scanning defense, and STIR/SHAKEN integration through TransNexus ClearIP, Neustar, and any HTTP-based signing service. Native TLS and SRTP encryption protect signaling and media on every call leg independently, and topology hiding conceals your internal infrastructure from external parties.
Where ProSBC goes further is programmability. Its Ruby-based routing script engine and REST API let you query external fraud databases, CNAM services, and billing systems during call setup, making real-time routing decisions based on fraud scores, caller identity, or any custom business logic your network requires. Validated integrations with TransNexus ClearIP, JeraSoft, SecureLogix, and YouMail extend your security perimeter with fraud intelligence that adapts to evolving threats.
ProSBC runs on AWS, Azure, VMware, KVM/Proxmox, and bare metal, scaling from 500 to 60,000 concurrent sessions per server, with subscription pricing starting at $1.25 per session per year. Deploy it yourself in under 20 minutes, or let TelcoBridges run it for you as a fully managed service.
